Yeah, I think something could be set up to fetch this information without needing too much resources, but at the same time it's not very useful info.
As far as giving direct access to server data, I think an API to get auction house info would not be exploitable at all as long as it was designed correctly, although I am aware it is MA we're talking about so they probably aren't very likely to make anything like this for lack of resources to do so, or misappropriation of resources into random side projects.
it would introduce a whole new security aspect to the backend servers... right now it's possible to go with an "accept all good" approach since all interaction is through the game interface, this is the safest way. But as soon as you expose the server to the outside then you can run the traffic through a proxy to modify the data and all kinds of fun.
I'm not saying it's impossible to do.. all I'm saying is that someone who's just curious might proxie your get request and instead post some injection script he's found online in a stack exchange forum and drops the entire db because MA apparently was running some unprotected rellic server they thought no one would access
let's take a VERY simplified SQL example of how a simple search might look:
pretend under_score names are columns and tables and camelCase are variables from whatever search is made to the auction
SELECT * FROM calypso_action WHERE (item_name LIKE '%itemName%')
and your request looks something like: GET
https://entropiaapi?itemName='bifrost'
This will of course generate a whole object with a shit ton of columns such as: name, dayli_markup,tt etc etc
by supplying " ')--" instead of "bifrost" we escape from the itemName value field and drop any other SQL used in the query that might cause our payload to crash.
as an example here's how you might bypass a simple login using the string " ' OR 1=1-- " as the "email":
SELECT * FROM users WHERE email=’’ OR 1=1--’ AND password=’123456’;
the -- lets us skip anything behind it so now the email only has to match or if 1 = 1 is true (which it is) it will simply take the first user in the table and log you in.... (this is probably the admin too)
we can now try to UNION another table after our result, table and column names can be derived from sys.tables, sys.columns in something like MYSQL I think and sqlite_master from sqlite any way doesn't matter same shit.
from there we might be able to find all kinds of fun information, maybe we can register an avatar with SQL syntax so when she collects missions and her name is prompted it's delivered and injected in an UPDATE that's meant to update user progress but instead we can spawn items or update our pedbalance as long as we know the column names and avatar ID's.
It's a bag'o worms with a potential for big profits if it turns out to be exploitable and making it not exploitable like you said is probably too costy
the above examples are kindergarden level SQL injections fyi.... not saying they're using SQL I'm just looking at potential exploits and these were the ones I could come up with at the top of my mind
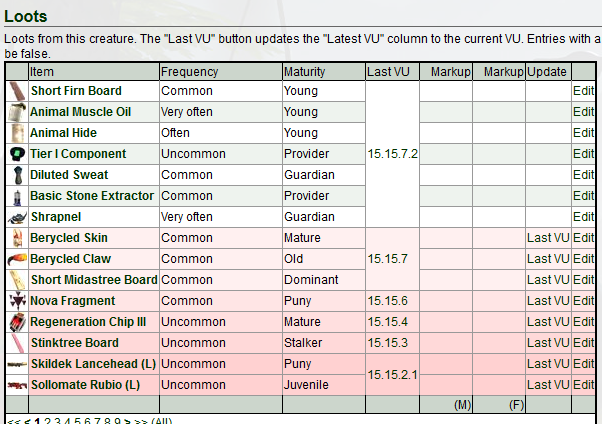
sorry for the long potato here's a post